APAC Crypto Licensing Is the New Singaporean Institutional Moat
Singapore's DTSP licensing framework did not thin the market by accident. Of the roughly 200 firms that had applied for or held provisional licenses before the June 30, 2025 deadline, industry analysts estimate 15 to 20 remain fully compliant. The rest exited, restructured, or stopped serving Singapore-connected customers. The framework was built to produce this exact result.
What this framework leaves is a jurisdiction with significantly less noise, a regulator that has been explicit about what it expects, and a compliance bar that functions as a market signal rather than a burden (for teams that can meet requirements) . Singapore's legal infrastructure, institutional banking relationships, and position in APAC are a signal to the broader market The firms operating there now are operating in a cleaner, more credible environment than what previously existed two years ago.
For funds and ecosystem programs with Singapore exposure, the real question is whether your portfolio teams can demonstrate the operational compliance that makes this jurisdiction work in their favour. That demonstration is specific, evidence-based and it starts with understanding exactly where the licensing perimeter sits.
The test is factual control, not branding
The test that determines licensing scope in APAC's current frameworks is not what a platform calls itself. Licensing is determined by who exercises factual control: who can move customer assets, who executes transactions, who approves listings, and where authority sits day to day.
Many companies thought they were exempt because they didn’t touch money, but MAS triggered licensing based on factual control, meaning if a Singapore based employee has the power to sign a transaction or move a token, the company was in scope.
The perimeter is wider than most teams initially assume, and the gap between their internal map and the regulator's map is where exposure lives:
- A wallet integration that enables asset transfers.
- A launchpad routing token distribution through a Singapore entity.
- A custodial staking product where the operator holds signing authority.
These activities are what trigger licensing requirements regardless of what the product page claims.
Operating in Singapore without the required DTSP license carries penalties of up to SGD 250,000 and up to three years' imprisonment. MAS has stated explicitly that it is unlikely to approve any application by an entity to provide digital token services from Singapore to only overseas persons, citing higher inherent money laundering and terrorist financing risks. For portfolio teams that built their Singapore structure assuming they could serve global customers from a Singapore entity, this is a direct market exit signal.
The litmus test is simple: if a supervisor asks who can move client assets today, can your team give a straightforward answer in one sentence?
Build your jurisdiction-by-product matrix before distribution decisions are made
Distribution support from an ecosystem program is not neutral. When a launchpad integration, listing partnership, or marketing amplification goes live, customer exposure scales and the licensing perimeter shifts. This often happens before the portfolio team has mapped what that shift actually means for their structure.
The tool that closes that gap is a jurisdiction-by-product matrix:
- - Which entity controls each product
- - Where customers are, where key staff sit
- - Where execution happens
- - Which entity signs contracts.
It answers the question regulators ask before the program manager does. For each product line there should be a clear answer on controlling entity, customer geography, and approval authority.
Programs that greenlight distribution support before that matrix is complete are underwriting a risk they have not priced. When a portfolio team needs to restructure quickly, the programs that supported them without documented scope are not insulated from the fallout.
The three jurisdictions below reflect the structures GVRN most commonly sees in portfolio company stacks: Singapore as the operational hub, Cayman and BVI as the entity layer. Scope classifications are illustrative and should be confirmed against current law for your specific structure and activity profile.
Design brief for matrix in below design content section - see below jpg and design in GVRN style

Adding a feature might be a relicensing event
Adding custody, yield, margin exposure, or market-making mandates each shifts the regulatory perimeter until proven otherwise. Most portfolio teams do not treat product expansion that way. The sequencing risk is that your token’s distribution channel is already live when they discover the licensing pathway requires months of operational buildout they did not plan for.
The BVI VASP framework makes this explicit: incomplete licensing submissions can be rejected, and applicants are expected to demonstrate governance, technology assurances, and risk and compliance frameworks before approval. This is often an operational buildout requiring time most teams have not planned for.
The practical fix is a designated internal trigger: product changes that expand the perimeter require legal sign-off before launch.
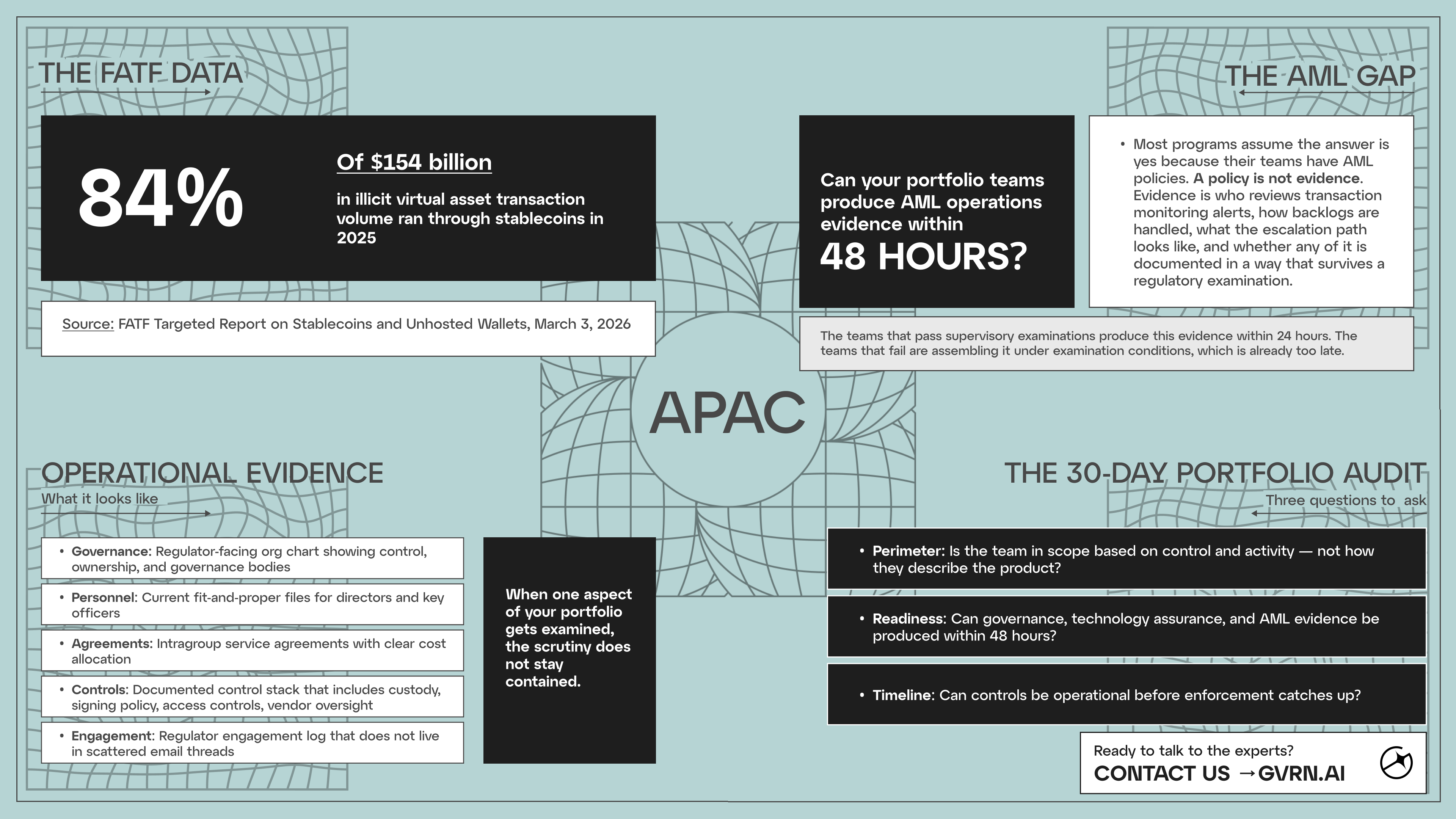
AML is moving from policy to operational evidence
The Financial Action Task Force’s (FATF's) March 2026 report on stablecoins and unhosted wallets put numbers to a risk that most ecosystem programs have been treating as theoretical.
Stablecoins accounted for 84% of the $154 billion in illicit virtual asset transaction volume in 2025. Vulnerabilities include peer-to-peer transactions via unhosted wallets that occur directly between individuals without a regulated intermediary, and difficulties stablecoin issuers face in controlling cross-chain activities that may fall outside counter-illicit finance controls.
Source: FATF Targeted Report on Stablecoins and Unhosted Wallets, March 3, 2026.
The operational question this raises is specific: do those policies translate into evidence on demand? For example, who reviews:
- Transaction monitoring alerts
- How backlogs are handled
- What the escalation path looks like when a high-risk pattern emerges
- Whether any of this is documented in a way that survives a regulatory examination
The teams that pass supervisory examinations produce this evidence within 24 hours. The teams that fail are assembling it under examination conditions, which is already too late. The difference is operating discipline, built before the examination cycle starts.
What operational evidence actually looks like
Licensing opens the compliance obligation rather than closing it: governance cadence, audits, incident reporting, compliance monitoring, recordkeeping. The teams that pass supervisory examinations are distinguished by being able to produce evidence on demand.
What that evidence looks like in practice:
- Regulator-facing organisational chart showing control, ownership, and governance bodies
- Current fit-and-proper files for directors and key officers
- Intragroup service agreements with clear cost allocation
- Documented control stack covering custody, signing policy, access controls, and vendor oversight.
- Regulator engagement log that does not live in scattered email threads.
If your program provides distribution, listings, or marketing support, regulatory scrutiny of a supported project does not stop there. Programs that cannot demonstrate consistent standards across their portfolio inherit the credibility problem, and the examination timeline is set by the regulator, not the program.
The 30-day audit
Any licensing-led portfolio audit should start with custody and exchange operations. This is where factual control is clearest, where licensing exposure is most direct, and where gaps surface fastest under examination. Start there, work outward across the portfolio, and for each team answer three questions.
Perimeter: Is the team in scope based on factual control and actual activity, not how they have described the product?
Readiness: Can the team produce governance, technology assurance, and AML operations evidence within 48 hours of a request?
Timeline: Can controls be implemented before enforcement catches up to current activity?
The programs that run this before a supervisor does are the ones that treat APAC licensing as operational infrastructure. The ones that don't run it first tend to discover the gaps under unfriendly and stressful conditions.
GVRN works with ecosystem programs to standardize portfolio audits, benchmark jurisdiction-by-product scope, and build supervisor-ready governance and compliance documentation. If APAC exposure is live in your portfolio, a pressure-test consultation is the right starting point.
Book at gvrn.ai.
FAQ for New Founders
What does APAC licensing mean for an accelerator or launchpad running a portfolio audit?
APAC licensing means the audit starts with activity, not incorporation. Where a team is registered tells you very little. What they do, who controls the assets, and where that control sits tells you whether they are in scope. The output of a useful audit is a jurisdiction-by-product matrix with controlling entity and customer geography mapped.
We do not touch user funds directly. Why does this apply to us?
The licensing perimeter follows activity, not intent. A launchpad that routes token distribution through a Singapore entity, a program that provides listing support to a custodial product, a liquidity program connected to a team with signing authority over user assets; each of these sits closer to the perimeter than most program managers assume when they first map it. The question is not whether you touch funds. It is whether the teams you support do, and whether your program's involvement amplifies that exposure.
How do we decide whether a portfolio team should pursue a license, restructure, or pause a market?
Three questions in sequence. Is the team in scope based on factual control and actual activity? Can they produce governance, technology assurance, and AML operations evidence within 48 hours of a request? Can controls be implemented before enforcement catches up to their current activity? The answer that is unclear is where the advisory conversation starts.
What does GVRN provide for ecosystem program managers navigating this?
Standardised portfolio audits, jurisdiction-by-product scope benchmarking across Singapore, Cayman, and BVI, and supervisor-ready governance and compliance documentation. The focus is on producing operational evidence, not policies, so that when a regulator or banking partner asks questions, the answers come from a single source of truth rather than a scramble across counsel, ops, and engineering.
Related Blogs
Browse all Blogs.svg)
Custos Bridge Pte Ltd (202303597M)
Version 1.2.0 | Checksum: F8A9–2034
Built from Singapore. Working globally.
Compliance, governance & legal architecture for protocols, DAOs, and founders.
.svg)
.png)
.png)